Your Host System is an Open Target. Time to Lock It Down.
No IAM. No Oversight. No Defense.
Host security hasn’t kept up with modern threats. Decentralized authentication, lack of access control, and no unified oversight leave host systems dangerously exposed.
The risks:
- Weak passwords are your only defense.
- No integration with enterprise identity and access management (IAM) solutions means no centralized control.
- No auditing creates security blind spots.
How users access your host system is a security gap—hackers exploit it. It’s time to fix it.
Why Traditional Host Security No Longer Works
Host security was built for a different era. Today’s cyber threats demand modern security frameworks.
The risks of leagacy host security:
- Authentication – Weak, static passwords make access easy to exploit.
- Authorization – Broad access permissions leave critical data unprotected.
- Auditing – Disconnected logs make compliance a nightmare.
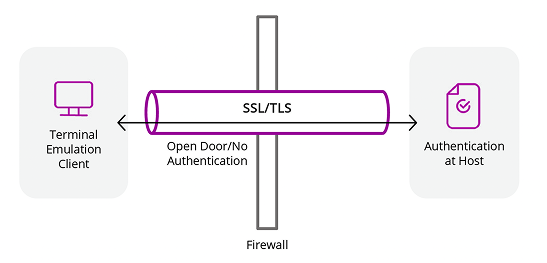
- Encryption – Even encrypted data is at risk without IAM oversight.
Without thoughtful IAM integration, host access remains exposed—lacking authentication, access control, and audit protection.
Don’t let outdated security leave your host system exposed. Get the full breakdown of the risks, challenges, and solutions in our expert whitepaper.
Modern Security Requires a Modern Approach
A modern approach to host connectivity should include:
- IAM-powered authentication – No more weak passwords.
- Granular access control – Ensure users get only the access they need.
- Centralized auditing – Gain full visibility for compliance and security.
- Seamless integration – No disruption to host applications.
Your host access security shouldn’t be the weak link.
Security threats won't wait. Why should you? Extend modern security frameworks to your host system today.
Related posts
Find Out How to Spot the Fake IT Worker
Rocket Software
1 min read
Cybercriminals aren’t always on the outside—some are already inside your organization.
Green Screens Are Under Attack. Fortify Your Mainframe Security.
Rocket Software
1 min read
If you still rely on basic passwords to enable access to terminal emulators, it could be the weakest link in your IT security.
Mainframe Passwords Are a Security Liability. Here’s a Fix.
Rocket Software
1 min read
Your mainframe security is only as strong as your weakest link—and static passwords are a hacker’s dream.