Green Screens Are Under Attack. Fortify Your Mainframe Security.
Your Terminal Emulator Could Be Your Weakest Link
Cyberattacks are surging, with AI-powered fraud, insider threats, and stolen credentials making green screen access a prime target. Yet, many organizations still rely on outdated terminal emulators—leaving the door wide open to cybercriminals.
If you still rely on basic passwords to enable access to terminal emulators, it could be the weakest link in your IT security. It’s time for a modern, password-free approach that protects without disrupting operations.
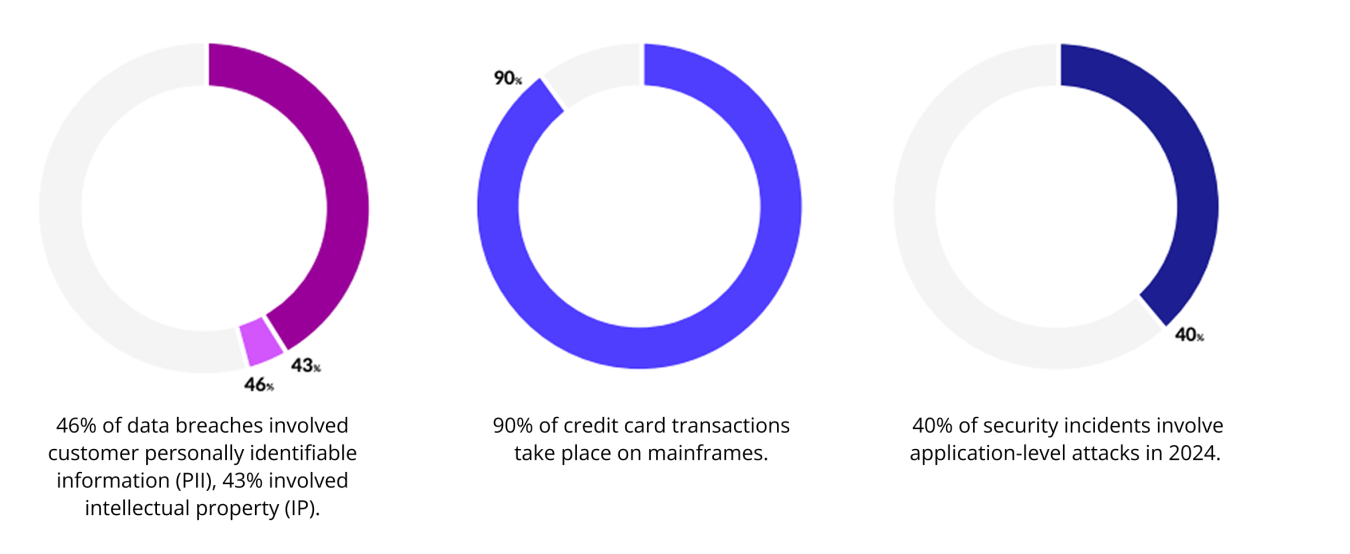
How vulnerable are you?
The 3 Biggest Security Threats to Your Mainframe
Security risks aren’t just about external hackers—new threats are emerging from AI, fake employees, and evolving regulations.
1. Insider threats and fake workers
Fraudulent employees and stolen credentials slip through the cracks, leading to security breaches. Lost, shared, or compromised credentials make it easier for attackers to infiltrate systems.
2. AI-powered attacks, ChatGPT, and automation
AI is supercharging credential theft and social engineering attacks. Cybercriminals use bots to mimic employees, bypass security, and infiltrate mainframes at alarming speed.
3. Compliance creep
Regulations like DORA, PCI DSS, and NYCRR Part 500 are tightening security requirements for mainframes. Organizations that fail to meet new standards face fines, breaches, and reputation damage.
5 Best Practices to Strengthen Mainframe Security
You don’t need a complete overhaul—just the right strategies. Here’s how leading enterprises are closing security gaps:
- Recognize green screens as high-risk – Protect them like any other critical asset.
- Integrate IAM and MFA – Leverage modern authentication to eliminate weak passwords.
- Use behavioral monitoring – Detect and block suspicious login activity.
- Establish a clear audit trail – Track every login, action, and access request.
- Choose security-first vendors – Ensure your terminal emulator meets modern security standards.
Unlike other solutions, Secure Host Access extends your enterprise identity and access management (IAM) best practices to secure host system connectivity.
And, for an added layer of defense in depth in your Zero Trust architecture, Secure Host Access fully integrates with IBM Z® MFA to enable complete multi-factor authentication on the host access as well as the host system itself.
Related posts
Find Out How to Spot the Fake IT Worker Hiding in Plain Sight
Rocket Software
2 min read
Cybercriminals aren’t always on the outside—some are already inside your organization.
Mainframe Passwords Are a Security Liability. Here's a Fix.
Rocket Software
2 min read
Your mainframe security is only as strong as your weakest link—and static passwords are a hacker’s dream.
Your Host System is an Open Target. Time to Lock It Down.
Rocket Software
1 min read
Host security was built for a different era. Today’s cyber threats demand modern security frameworks.