Find Out How to Spot the Fake IT Worker Hiding in Plain Sight
Insider Threats Are Rising. Are You Prepared?
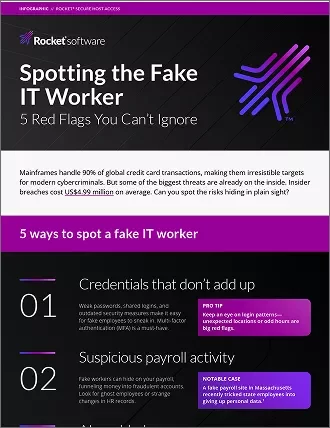
Cybercriminals aren’t always on the outside—some are already inside your organization. Disguised as employees or contractors, fake IT workers can slip through security gaps, leading to costly breaches.
The impact? Massive financial loss and high-risk exposure.
$4.99M
the average cost of an insider breach.
90%
of global credit card transactions rely on mainframes—prime targets for cybercrime.
5 Red Flags You Can’t Ignore
- Credentials that don't add up - Weak passwords and shared logins create an open door for cybercriminals.
- Suspicious payroll activity – Fake workers funnel money through ghost accounts.
- AI-enabled scams – Attackers use deepfake profiles and phishing to gain access.
- Insider threats – Disgruntled employees or contractors can do serious damage.
- Compliance gaps – Failing to meet GDPR and DORA regulations can be costly.
How to Protect Your Mainframe
- Secure access – Prevent unauthorized logins with multi-factor authentication.
- Monitor activity – Track system access to detect suspicious behavior early.
- Leverage IAM – Control who gets access to critical systems with ease.
Stop insider threats before it's too late.
Related posts
What is 23 NYCRR 500 and is Your Organization Compliant?
Rocket Software
2 min read
In 2017, the New York State Department of Financial Services (NYDFS) established 23 NYCRR 500, a cybersecurity regulation that set out specific requirements for financial services businesses in the state of New York.
Bringing Secure Host Access to the Green Screen
Rocket Software
3 min read
As IT infrastructure matures, so do security threats. And with more businesses leveraging remote access tools to support enterprise operations, attackers have taken advantage of new opportunities to cause serious damage.
Securing terminal emulation and green screen access from evolving threats
4 min read
In the face of a constantly shifting threat landscape, securing terminal emulation and green screen access is critical to security and compliance.